When disaster strikes, unscrupulous actors come out of the woodwork. They prey on the general confusion and desperation. Ruth King, profitability master with HVACChannel.TV, said this unfortunately happens all the time after events such as hurricanes. The COVID-19 pandemic is proving no different.
One of the biggest concerns for HVAC contractors right now is access to funding. An online poll currently running on The ACHR NEWS website finds nearly half of respondents are seeing major slowdowns to their business, with 20 percent saying they might have to shut their doors. The federal government has announced billions of dollars’ worth of financial support through various programs, including loans backed by the Small Business Administration.
However, banks warn that quick implementation of the SBA financing programs will prove challenging. Scam artists are taking advantage of the need for fast funding.
SCAM ARTISTS USE EMAIL, PHONE CALLS TO TARGET THOSE SEEKING SBA LOANS
The Federal Trade Commission has issued several warnings about scams targeting small businesses seeking financing. One common scam comes in the form of an email. The FTC warns that scam artists have “been known to copy logos of financial institutions and government agencies, including the SBA, and use wording that sounds familiar. They also manipulate email addresses so that a message looks to be from a legitimate source — but isn’t.” The emails might come with a link that claims to take the recipient to a bank or government agency site — but instead unleashes malware. HVAC contractors should start the process to obtain SBA lending by going directly to the agency’s site, sba.gov.
Other scam artists use phone calls to reach their intended target. The FTC has heard reports of small business owners receiving calls from scam artists claiming they can speed up the SBA funding process. Others claim to represent a legitimate bank. Some of these scam artists seek upfront fees. Others want personal information, such as Social Security numbers and tax IDs. The FTC advises owners to contact their banks directly on a known number before giving out any sensitive information.
Potential problems reach into customer financing as well. King warns about outfits such as fly-by-night consumer creditors. If an entity if federally regulated, such as a bank or credit union, that’s one thing. If the company offering to finance an HVAC contractor’s customers is one the contractor has never heard of and can’t find information about, be wary.
“Make sure you’re dealing with someone who is legit,” King said.
FTC COMMISSIONER WARNS OF RISKS WITH MERCHANT CASH ADVANCES
HVAC contractors also need to use caution with legal but lightly regulated finance sources. FTC Commissioner Rohit Chopra recently warned about the risks involved in using merchant cash advance (MCA) firms for financing. An MCA provides a lump sum for a business’ current needs in exchange for future receivables. The practice started among traditional retailers, but expanded following the financial crisis and is now used by a wide range of businesses, including contractors.
Because these deals aren’t really loans or other traditional installment contracts, they fall outside most finance laws and lack a defined regulator. Federal agencies, such as the Consumer Financial Protection Bureau, and state attorneys-general have taken legal action against MCA firms in recent years. Chopra and other accuse these firms of charging high rates and using stern collection practices, including lawsuits. The industry counters that its rate and practices reflect the high level of risk it takes on when providing funds. Either way, contractors need to understand any agreement into which they enter.
SHELTER IN PLACE ORDERS CREATE NEW CHALLENGES
The current shelter-in-place orders in effect across the nation create more opportunities for scam artists. Many HVAC contractors have staff working from home during this crisis, and that creates more opportunities for scam artists. There have been numerous reports of scam artists exploiting vulnerabilities in the popular teleconferencing software from Zoom Video Communications Inc. many are using for video conferencing. Some of this comes in the form of bad-taste pranks, such as hackers bombing the Laguna Beach City Council meeting with pornography.
However, Check Point Software Technologies Ltd. warns the same techniques can be used to eavesdrop on private meetings to obtain sensitive data. In addition, the online security firm warns that hundreds of new domains registered in the past few weeks contain the word “zoom,” with about four percent of these found to contain what Check Point calls “suspicious characteristics.” These sites could be part of a phishing scam, or they could infect systems with malware. The actual site is zoom.us.
The problems aren’t limited to Zoom, although that software has the highest profile right now. The FBI warns that any telecommunication software is a target of cyber criminals. This includes software used for educational purposes. With many business owners and employees using general computers these days and sharing them with other family members, the risk is higher than usual.
HVAC CONTRACTORS MUST STAY IN TOUCH, STAY AWARE
Having employees disbursed from the main office also increases the risk from popular phishing scams. One of the most common involves a spoofed email from the owner or other manager, telling employees of an immediate need for cash. The scam artists instructs the employees to transfer money via a wire service or cash app. This threat makes communication crucial during this time.
Business owners should always make sure they are aware of the latest scams, but now it’s more important than ever. There are a number of online resources to help them with this. The FTC offers regular updates on scams, as do the websites of each state’s attorney-general. The IRS posted a list of common scams here. The Better Business Bureau also offers scam updates here. Contractors can also set up alerts that gather stories from various news sources.
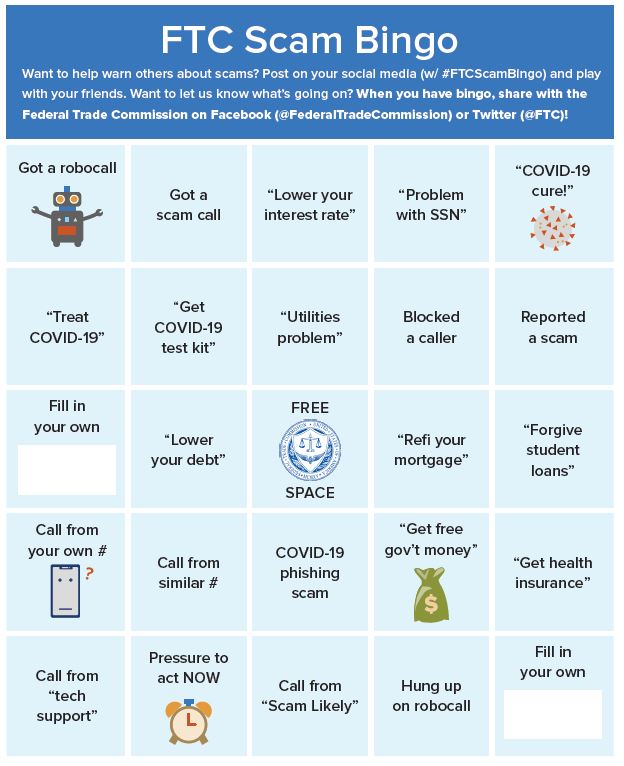
Click the graphic to download as a PDF
There are so many scams related to the COVID outbreak that the Federal Trade Commission created this bingo card to promote awareness.
TIPS TO PROTECT YOU AND YOUR ORGANIZATION
Teleworking Tips:
Do:
- Select trusted and reputable telework software vendors; conduct additional due diligence when selecting foreign-sourced vendors.
- Restrict access to remote meetings, conference calls, or virtual classrooms, including the use of passwords if possible.
- Beware of social engineering tactics aimed at revealing sensitive information. Make use of tools that block suspected phishing emails or allow users to report and quarantine them.
- Beware of advertisements or emails purporting to be from telework software vendors.
- Always verify the web address of legitimate websites or manually type it into the browser.
Don't:
- Share links to remote meetings, conference calls, or virtual classrooms on open websites or open social media profiles.
- Open attachments or click links within emails from senders you do not recognize.
- Enable remote desktop access functions like Remote Desktop Protocol (RDP) or Virtual Network Computing (VNC) unless absolutely needed.1
Education Technology Tips:
School districts across the United States are working to address a dynamically changing learning environment. The FBI acknowledges everyone is adjusting to these demands, but the FBI encourages parents and families to:
Do:
- Closely monitor children's use of edtech and online services.
- Research edtech service user agreements about data breach notifications, marketing, and/or selling of user data, data retention practices, and whether users and/or parents can elect to have student data deleted by request.
- Conduct regular internet searches of children's information to monitor the exposure and spread of their information on the internet.
- Consider credit or identity theft monitoring to check for any fraudulent use of their child's identity.
- Research parent coalition and information-sharing organizations available online for those looking for support and additional resources.
- Research school-related, edtech, and other related vendor cyber breaches, which can further inform families of student data and security vulnerabilities.
Don't:
- Provide exact information on children when creating user profiles (e.g., use initials instead of full names, avoid using exact dates of birth, avoid including photos, etc.)
BEC Tips:
Do:
- Check for last-minute changes in wiring instructions or recipient account information.
- Verify vendor information via the recipient's contact information on file—do not contact the vendor through the number provided in the email.
- Verify the email address used to send emails, especially when using a mobile or handheld device, by ensuring the sender's email address appears to match who it is coming from.
- If you discover you are the victim of a fraudulent incident, immediately contact your financial institution to request a recall of funds, and contact your employer to report irregularities with payroll deposits. As soon as possible, file a complaint with the FBI's Internet Crime Complaint Center at www.ic3.gov or, for BEC and/or email account compromise (EAC) victims, BEC.IC3.gov.
Cyber Crime Vulnerability Tips:
The following tips can help protect individuals and businesses from being victimized by cyber actors:
Do:
- Verify the web address of legitimate websites and manually type them into your browser.
- Change passwords for routers and smart devices from default setting to unique passwords.
- Check for misspelled domain names within a link (for example, confirm that addresses for government websites end in .gov).
- Report suspicious activity on work computers to your employer.
- Use multi-factor authentication (MFA) when accessing organizational sites, resources, and files.
- Practice good cyber security when accessing Wi-Fi networks, including use of strong passwords and Wi-Fi Protected Access (WPA) or WPA2 protocols.
- Ensure desktops, laptops, and mobile devices have anti-virus software installed and routine security updates are applied; this includes regularly updating web browsers, browser plugins, and document readers.
Don't:
- Open attachments or click links within emails received from senders you do not recognize.
- Provide usernames, passwords, birth dates, social security numbers, financial data, or other personal information in response to an email or phone call.
- Use public or non-secure Wi-Fi access points to access sensitive information.
- Use the same password for multiple accounts.
See more articles from this issue here!





Report Abusive Comment